What kind of tools?
We have a long history of software development for CSIRTs. Here’s a small sample of the types of tools we’ve built before and can build for you, too.
Monitoring systems 
Does your team follow up the status of resources being abused? What happens to that phishing site after you logged it? Rather than your analysts continually checking - if they remember - it’s far better to automate and systemise this process.
Using our monitoring systems, not only can you see the current status of a bad URL or host, but also its complete history. Don’t just check and forget: learn how scammers operate.
Data processing and sharing 
One thing security teams don’t lack is mountains of data. One thing they often lack are tools to break that data down and understand it.
CSIRTs have large collections of information: domain name records, IP addresses, web page data, malware, C&C data and more. Only by learning how incidents relate together can we come up with the insights to improve our response.
Using both traditional data storage technologies as well as more cutting edge technologies, we can help you take control of your data and understand it on a deeper level.
Visualisation 
Even when we’ve found our linkages and relationships, these are less useful if our analysts can’t easily see and take action on them. Enter visualisations.
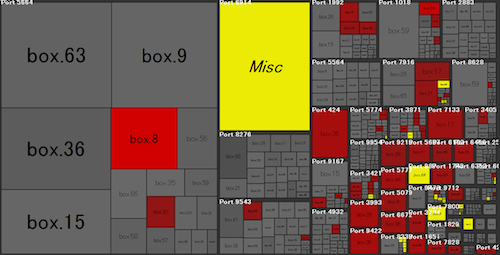
Visualisations can be as simple as a graph, or as complex as 3D eye candy that will impress the top brass. We believe visualisations need to meet the following attributes:
- Simple - a visualisation should be understandable with little instruction.
- Automatic - a visualisation will be forgotten if it needs any human involvement to be updated.
- Interactive - we now have amazing web technogies that let us do highly functional interfaces. Static graphs don’t quite cut it any more.
- Attractive - we like to deny it, but tools with shoddy interfaces are often dismissed in favour of those where the polish is obvious. We make sure the quality of the interface matches the quality of the results.
- Useful - most important of all, a visualisation should fill an operational need, not just be pretty to look at.
Workflow tools 
A small incident response team often feels like they need to take care of everything, from database admin, to trawling through TCP dump logs, to automating emails to victims of a mass compromise. We love writing small, simple tools that take the load off your analysts. Don’t be a victim of multitasking - let us help you automate the small things and reduce the load on your team.